If you are working in DevOps, cloud, platform engineering, or security, Kubernetes security is no longer optional. Teams are moving fast, clusters are growing, and risks are increasing at the same time. That is why the Certified Kubernetes Security Specialist (CKS) has become one of the most useful certifications for engineers and managers who want stronger cloud-native security skills.This guide is written for working engineers, software professionals, and managers in India and globally. It explains what CKS is, who should take it, what you will learn, how to prepare, what mistakes to avoid, and how to build a long-term certification path around it. It also includes role-based certification mapping, learning paths, FAQs, and next-step certification suggestions.The DevOpsSchool CKS certification page describes the course as an industry-recognized online training and highlights its CKS focus areas, including cluster setup, hardening, supply chain security, and runtime security topics.
Why CKS Matters Today
Kubernetes is now used for production systems in startups, enterprises, and regulated industries. As adoption grows, the attack surface also grows. Security issues are no longer limited to a single VM or a single app. They can happen in:
- Cluster configuration
- Control plane access
- Node hardening
- Secrets handling
- Container images
- Supply chain pipelines
- Runtime behavior
- Monitoring and audit logs
The DevOpsSchool CKS page explains that CKS is designed for professionals securing Kubernetes environments and emphasizes practical security topics across build, deployment, and runtime.
For managers, this certification is useful because it helps identify engineers who can reduce production risk. For engineers, it is useful because it improves real hands-on security thinking, not just theory.
What Is Certified Kubernetes Security Specialist (CKS)?
The DevOpsSchool CKS page describes CKS as a Kubernetes security-focused certification and notes that it is aimed at professionals responsible for securing Kubernetes environments such as administrators, cloud administrators, and security specialists.
In simple words, CKS is for people who want to answer questions like:
- How do I harden a Kubernetes cluster?
- How do I reduce container risks?
- How do I secure secrets and service accounts?
- How do I improve runtime detection and auditability?
- How do I secure the software supply chain in Kubernetes environments?
It is a very practical certification path for people already working close to Kubernetes or planning to move into DevSecOps/platform security roles.
Quick Snapshot of the DevOpsSchool CKS Training
The DevOpsSchool CKS page shows the following course-level details:
- Course title: Certified Kubernetes Security Specialist (CKS) Certification Training Course
- Training format: Online Training
- Duration: 10–15 hours
- Certification: Industry recognized
- Target audience includes DevOps engineers, SREs, security engineers, cloud administrators, and others working on Kubernetes security.
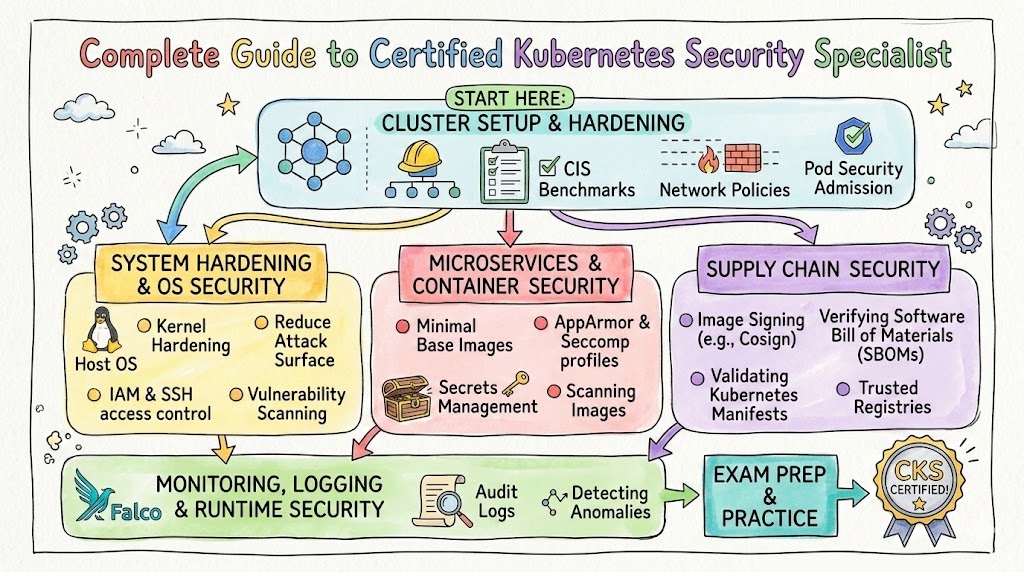
It also lists agenda areas such as:
- Cluster Setup
- Cluster Hardening
- System Hardening
- Minimizing Microservice Vulnerabilities
- Supply Chain Security
- Monitoring, Logging and Runtime Security
These are exactly the kinds of skills employers look for when they want engineers who can operate Kubernetes securely in production.
Certification Table
Below is a practical table centered on the certification in this guide, while also showing recommended next-step options (same track, cross-track, leadership) so readers can plan progression.
Note: Only the official certification links provided in your prompt are included.
| Certification | Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
|---|---|---|---|---|---|---|
| Certified Kubernetes Security Specialist (CKS) | Kubernetes Security / DevSecOps | Advanced | DevOps Engineers, SREs, Platform Engineers, Cloud Engineers, Security Engineers, Engineering Managers (oversight) | Kubernetes basics, Linux basics, kubectl use, cluster concepts, workload deployment experience | Cluster hardening, system hardening, RBAC, network policies, secrets, supply chain security, runtime security, logging & audit practices | 1 (for Kubernetes security-focused path after Kubernetes basics) |
| Master in DevOps Engineering (MDE) | DevOps + DevSecOps + SRE | Broad Program / Professional | Engineers and managers who want a wider roadmap across DevOps, DevSecOps, and SRE | Basic IT/software/system knowledge | Multi-discipline DevOps, DevSecOps, SRE concepts, tools, workflows, job-ready skills | Cross-track / broader foundation or leadership path |
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What it is
Certified Kubernetes Security Specialist (CKS) is a security-focused Kubernetes certification for professionals who need to secure containerized workloads and Kubernetes platforms. It validates practical knowledge around cluster hardening, system hardening, microservice security, supply chain protection, and runtime monitoring/security.
Who should take it
- DevOps Engineers working on Kubernetes deployments
- Site Reliability Engineers (SREs)
- Platform Engineers managing internal Kubernetes platforms
- Cloud Engineers operating container platforms
- Security Engineers moving into cloud-native security
- Application teams deploying to Kubernetes and needing secure defaults
- Technical leads and engineering managers who oversee Kubernetes programs
The DevOpsSchool CKS page’s target audience section also includes many of these profiles, including DevOps engineers, SREs, cloud admins, and security-focused professionals.
Skills you’ll gain
- Securing Kubernetes cluster access and API exposure
- Applying RBAC to reduce unnecessary permissions
- Managing service accounts safely
- Implementing network security policies
- Hardening nodes and reducing OS attack surface
- Working with kernel hardening tools (for example AppArmor / seccomp concepts)
- Managing Kubernetes secrets more securely
- Reducing microservice and container runtime vulnerabilities
- Improving image and supply chain security practices
- Using logging and audit mechanisms for visibility and response
- Improving runtime security posture for containers
These topics are strongly reflected in the CKS course features, objectives, and agenda listed on the DevOpsSchool page.
Real-world projects you should be able to do after it
- Harden a Kubernetes cluster baseline
Apply access controls, reduce exposure, and create safer defaults for a production-ready environment. - Build a namespace security model
Use RBAC roles and role bindings, service account restrictions, and workload isolation patterns. - Implement network segmentation for microservices
Use network policies to limit east-west traffic and reduce blast radius. - Secure secrets handling in a deployment pipeline
Replace weak secret practices, reduce plaintext handling, and improve access controls. - Create a container image validation and scanning workflow
Build a basic supply chain process that checks images before deployment. - Enable audit logging and incident visibility
Improve traceability for access and suspicious events. - Design a runtime hardening checklist for platform teams
Create a reusable checklist that can be applied across clusters and projects.
Preparation plan (7–14 days / 30 days / 60 days)
7–14 days plan (for experienced Kubernetes users)
Best for engineers already working daily on Kubernetes.
- Day 1–2: Review Kubernetes security fundamentals and exam domains
- Day 3–4: Cluster setup + hardening topics
- Day 5–6: System hardening + node/container runtime controls
- Day 7–8: Secrets + microservice vulnerabilities + network policies
- Day 9–10: Supply chain security (images, registry controls, scanning flow)
- Day 11–12: Logging, audit, runtime security
- Day 13–14: Full hands-on revision and timed practice tasks
Goal: Speed + accuracy under pressure.
30 days plan (recommended for most working engineers)
Best for busy professionals balancing job + study.
- Week 1: Kubernetes refresh (pods, deployments, services, namespaces, RBAC basics)
- Week 2: Cluster hardening + system hardening
- Week 3: Microservice vulnerabilities + secrets + network security
- Week 4: Supply chain + runtime security + mock practice + weak-area revision
Study rhythm suggestion
- Weekdays: 60–90 minutes
- Weekends: 3–4 hours hands-on labs
Goal: Strong understanding + repeatable hands-on execution.
60 days plan (best for career switchers / beginners to K8s security)
Best for people who know DevOps/cloud basics but are newer to Kubernetes security.
- Days 1–15: Kubernetes basics and admin workflow refresh
- Days 16–30: Security domains overview + labs
- Days 31–45: Deep practice by domain (hardening, secrets, policies, runtime)
- Days 46–55: Integrated scenarios and troubleshooting
- Days 56–60: Mock runs, revision notes, final confidence pass
Goal: Build both Kubernetes confidence and security decision-making.
Common mistakes (bullets)
- Studying only theory and skipping hands-on practice
- Ignoring Linux/system hardening basics
- Memorizing commands without understanding why they are used
- Weak RBAC understanding (over-permissioning everything)
- Not practicing network policy troubleshooting
- Not revising secrets and service account handling
- Treating supply chain security as “just image scanning”
- Ignoring runtime visibility and audit logs
- No timed practice before final attempt
- Trying to learn Kubernetes and advanced security at the same speed in a very short time
Best next certification after this
A smart next step depends on your goal:
- Same track (Kubernetes security depth): Continue with advanced cloud/platform security projects and Kubernetes security specialization work (practical depth path)
- Cross-track (broader engineering value): Move into the Master in DevOps Engineering (MDE) for broader DevOps + DevSecOps + SRE coverage
- Leadership path: Take a broader architecture/management-oriented DevOps track and combine CKS skills with governance, platform strategy, and reliability ownership via MDE
The MDE page explicitly positions the program around DevOps, DevSecOps, and SRE together, which makes it a strong cross-track or leadership expansion option for CKS holders.
What You Actually Learn in CKS
The DevOpsSchool CKS agenda is useful because it shows the real skill blocks you should master. Below is a practical interpretation of those agenda items.
1) Cluster Setup Security
This is about building a secure base from the beginning. If the foundation is weak, later controls will not fully protect the environment.
Key focus areas include:
- Restricting cluster-level access
- Safer ingress setup
- Reducing exposure of node metadata/endpoints
- Verifying platform binaries before deployment
- Avoiding unnecessary GUI usage in sensitive environments
This matters because early setup decisions create long-term security debt.
2) Cluster Hardening
This is where you reduce what attackers can do if they gain access.
Typical outcomes:
- Safer Kubernetes API access controls
- Better RBAC design
- Service account permission minimization
- Regular update discipline for Kubernetes components
This is one of the most valuable CKS skill blocks for platform and SRE teams because it directly reduces blast radius.
3) System Hardening
Kubernetes security is not only Kubernetes YAML. It also includes host and runtime-level thinking.
You should learn how to think about:
- Host OS footprint reduction
- IAM role minimization
- External network exposure minimization
- Kernel hardening tools and runtime boundaries
This skill block is especially useful for platform engineers and security engineers supporting production infrastructure.
4) Minimizing Microservice Vulnerabilities
Most teams focus on deployment speed. CKS pushes you to also focus on secure service design and deployment guardrails.
Important areas include:
- OS-level security domains
- Secrets management
- Multi-tenant runtime sandboxing concepts
- Pod-to-pod encryption approaches like mTLS (concept and implementation direction)
This helps application and platform teams work together instead of treating security as a last-minute review.
5) Supply Chain Security
This is now a major risk area in cloud-native delivery.
Practical focus:
- Smaller, safer base images
- Registry controls / whitelisting
- Image signing and validation concepts
- Static analysis for workloads and Dockerfiles
- Vulnerability scanning
A strong engineer in this area can improve both security and release confidence.
6) Monitoring, Logging, and Runtime Security
Prevention alone is not enough. You also need detection and response visibility.
CKS-aligned runtime thinking includes:
- Behavioral monitoring
- Threat detection across infra, apps, and workloads
- Audit logs for access tracking
- Runtime immutability practices for containers
This is where CKS becomes very valuable for SRE and incident response collaboration.
Choose Your Path
This section is designed for people who ask: “I want CKS, but how do I fit it into my career path?”
1) DevOps Path
Goal: Build and operate secure CI/CD + Kubernetes delivery systems.
Recommended sequence
- DevOps fundamentals (CI/CD, IaC, containers, Linux)
- Kubernetes operations basics
- CKS
- Broader DevOps/DevSecOps/SRE program (MDE) for scale and architecture thinking
Why CKS helps here
DevOps teams often own deployment pipelines and cluster changes. CKS adds strong security discipline to automation.
2) DevSecOps Path
Goal: Shift security left and secure cloud-native delivery end to end.
Recommended sequence
- DevOps + Linux + containers basics
- Kubernetes fundamentals
- CKS
- Broader DevSecOps concepts and program expansion (MDE cross-track path)
Why CKS helps here
CKS directly supports security in build, deploy, and runtime phases, which is core to DevSecOps practice.
3) SRE Path
Goal: Keep services reliable and secure in production.
Recommended sequence
- Linux + networking + observability basics
- Kubernetes admin/operations comfort
- CKS
- SRE-focused reliability and production engineering expansion (via MDE breadth and SRE practice)
Why CKS helps here
SREs need to balance reliability and security. CKS gives stronger production guardrails and response readiness.
4) AIOps / MLOps Path
Goal: Secure ML platforms and Kubernetes-based AI workloads.
Recommended sequence
- MLOps platform basics (containers, orchestration, pipelines)
- Kubernetes deployment for ML workloads
- CKS
- MLOps/AIOps tooling specialization
Why CKS helps here
AI/ML pipelines often run on shared Kubernetes infrastructure. Security controls, image safety, and runtime visibility become critical.
5) DataOps Path
Goal: Secure data pipelines and services running on containers/Kubernetes.
Recommended sequence
- Data pipeline fundamentals + cloud basics
- Containers + Kubernetes basics for data workloads
- CKS
- DataOps workflow automation and governance specialization
Why CKS helps here
Modern data services increasingly use Kubernetes. CKS helps secure data services, secrets, and runtime environments.
6) FinOps Path
Goal: Optimize cloud cost with secure, reliable platform operations.
Recommended sequence
- Cloud + cost management basics
- Kubernetes cost and workload patterns
- CKS (for secure governance context)
- FinOps practice + reporting + policy enforcement
Why CKS helps here
Security and cost are connected. Poor security design can increase operational costs, incident costs, and compliance overhead.
Role → Recommended Certifications Mapping
Below is a practical mapping for the roles you requested. This helps managers and individuals build a realistic certification journey.
| Role | Primary Need | Recommended First Focus | Where CKS Fits | Recommended Broader Path |
|---|---|---|---|---|
| DevOps Engineer | Delivery automation + platform ops | Kubernetes basics + CI/CD + Linux | Core (very valuable if working on K8s) | Add MDE for DevOps/DevSecOps/SRE breadth |
| SRE | Reliability + production operations | Observability, Linux, networking, Kubernetes ops | Core (security hardening + runtime visibility) | Add broader SRE/DevOps program (MDE path) |
| Platform Engineer | Internal platform design and guardrails | Kubernetes administration + platform standards | Core (cluster hardening, RBAC, policy design) | Add MDE for multi-discipline architecture |
| Cloud Engineer | Cloud infrastructure + container operations | Cloud + containers + K8s operations | Strong (especially for managed K8s environments) | Add MDE for cross-team delivery/security/reliability |
| Security Engineer | Cloud-native security controls | Container security + Kubernetes basics | Core / High priority | Add DevSecOps breadth and platform collaboration |
| Data Engineer | Secure data workloads on cloud platforms | Containers + orchestration basics | Helpful when data platforms use K8s | Add DataOps specialization + platform security awareness |
| FinOps Practitioner | Cost visibility and governance | Cloud billing, usage analytics, architecture basics | Helpful (governance awareness, secure operations context) | Add FinOps specialization + platform governance |
| Engineering Manager | Team capability planning + risk reduction | Team skill mapping + platform understanding | Strategic (great for evaluating team readiness) | MDE useful for broader cross-functional planning |
Next Certifications to Take
You specifically asked for three next-step options: same track, cross-track, leadership. Here is a clean version for blog readers.
1) Same Track (Depth Path)
Goal: Become the go-to Kubernetes security engineer in your team.
- Continue with deeper Kubernetes platform security projects
- Build production hardening templates, baseline policies, and audit playbooks
- Lead internal platform security reviews
Best for: Security Engineers, Platform Engineers, SREs, senior DevOps Engineers
2) Cross-Track (Broaden Your Value)
Goal: Add DevOps + DevSecOps + SRE context around Kubernetes security.
- Move into Master in DevOps Engineering (MDE) as a broader path
- Learn how security integrates with delivery speed and reliability
- Build stronger architecture decision-making skills
The MDE page explicitly frames the program as covering DevOps, DevSecOps, and SRE together, making it a strong cross-track expansion after CKS.
3) Leadership Path (Technical + Management Growth)
Goal: Move from “implementer” to “owner of platform standards.”
- Use CKS knowledge to define secure Kubernetes standards
- Build review checklists for teams
- Align security, reliability, and release speed across engineering
- Use a broader program like MDE to understand team-wide capability planning
Best for: Tech Leads, Engineering Managers, Platform Managers, Security Leads
How Managers Should Use CKS in Team Planning
Many managers ask, “Should I sponsor this certification for my team?” The answer is often yes, if your team uses Kubernetes in production.
CKS is especially useful when your team has these problems:
- Too many cluster admins with broad access
- No clear RBAC model
- Secrets handled in unsafe ways
- Weak container image controls
- No runtime visibility beyond basic logs
- Security reviews happening too late in release cycles
Team-level outcomes you can expect
- Better hardening practices
- Better access control hygiene
- Stronger delivery confidence
- Better alignment between DevOps, SRE, and Security teams
- Lower risk of common Kubernetes misconfiguration issues
For engineering managers, CKS is not just a certification. It is a capability-building investment.
Top Institutions / Brands That Provide Help in Training cum Certifications for CKS
Below is a short, practical overview of the institutions/brands you listed. This section is written in a neutral guidance style for readers who are comparing training ecosystems.
DevOpsSchool
DevOpsSchool is a well-known training brand in the DevOps and cloud ecosystem and provides a dedicated CKS certification training page with agenda, target audience, and learning details. It is useful for learners who want structured, instructor-led support and a certification-oriented pathway. The provided CKS page also highlights online training, industry-recognized certification, and a curriculum aligned to CKS security domains.
Cotocus
Cotocus is commonly seen in the same learning ecosystem and is often considered by learners looking for practical DevOps and cloud support exposure. It can be useful for professionals who want hands-on learning orientation and industry-use-case discussions alongside formal training.
ScmGalaxy
ScmGalaxy has long been associated with DevOps/tooling education and is often referenced by learners who want foundational and intermediate skill-building support. It may be useful for those who need a stepping stone before moving into advanced Kubernetes security topics like CKS.
BestDevOps
BestDevOps is often considered by learners comparing certification-oriented training providers in the DevOps space. It is generally useful for people who want guided courses, structured modules, and exam-focused learning support.
DevSecOpsSchool
For learners specifically focused on security in DevOps pipelines and cloud-native systems, DevSecOpsSchool is a relevant brand in the ecosystem. It can be a useful companion path for people taking CKS and then wanting broader DevSecOps practices beyond Kubernetes.
SRESchool
SRESchool is relevant for professionals working in reliability engineering and production operations. Since CKS overlaps with runtime security, monitoring, and operational hardening, SRE-oriented learners may benefit from combining SRE practices with Kubernetes security training.
AIOpsSchool
AIOpsSchool becomes relevant when organizations run modern AI/ML infrastructure on containerized or Kubernetes-based platforms. Learners in platform and operations roles may use this path to combine automation, observability, and operational intelligence with stronger security basics.
DataOpsSchool
DataOpsSchool is useful for data professionals and platform teams operating data pipelines at scale. As more data workloads move to cloud-native environments, Kubernetes security awareness becomes increasingly valuable for data platform reliability and protection.
FinOpsSchool
FinOpsSchool is useful for professionals focused on cloud cost optimization and governance. While CKS is security-focused, FinOps practitioners working closely with platform teams can benefit from understanding secure platform controls that influence operational and compliance costs.
Common Career Outcomes After CKS (Practical View)
CKS by itself does not guarantee a job. But it can strongly improve your profile when combined with real Kubernetes work.
What changes after CKS for many professionals
- You can speak more confidently in security reviews
- You can design safer Kubernetes deployment standards
- You can troubleshoot security-related Kubernetes issues faster
- You become more useful in cross-team discussions (DevOps + Security + SRE)
- You can move toward platform security or cloud-native security responsibilities
Roles where CKS adds direct value
- DevOps Engineer (Kubernetes-heavy)
- Platform Engineer
- SRE
- Cloud Security Engineer
- DevSecOps Engineer
- Kubernetes Administrator with security responsibilities
FAQ
1) Is CKS difficult for working engineers?
Yes, it can be challenging because it is security-focused and practical. It is easier for engineers who already work with Kubernetes regularly.
2) Can a beginner take CKS directly?
A complete beginner in Kubernetes may struggle. It is better to first build Kubernetes basics, then move into CKS.
3) How much time should I prepare for CKS?
It depends on your current level. A strong Kubernetes engineer may prepare in 7–14 days, while most professionals do better with a 30-day plan. Career switchers may need 60 days.
4) Is CKS useful for managers?
Yes, especially engineering managers and platform/security managers. It helps them understand what secure Kubernetes operations actually require, even if they do not do daily hands-on tasks.
5) Is CKS only for security engineers?
No. It is also highly useful for DevOps Engineers, SREs, Platform Engineers, and Cloud Engineers who manage Kubernetes environments.
6) What should I learn before CKS?
You should know basic Kubernetes objects, kubectl usage, namespaces, deployments, services, and Linux basics. Some networking knowledge also helps.
7) Should I do CKS before or after broader DevOps training?
If your job is already Kubernetes-focused, CKS can come early. If you need broader DevOps, DevSecOps, and SRE coverage, combine it with a broader path like MDE.
8) Does CKS help in DevSecOps roles?
Yes. CKS aligns strongly with DevSecOps because it covers security in build/deploy/runtime workflows for cloud-native systems.
9) Is CKS good for SRE professionals?
Yes. SREs benefit from CKS because production reliability and security are closely connected, especially in Kubernetes systems.
10) Can I prepare for CKS while working full time?
Yes. A 30-day plan with consistent weekday and weekend study blocks works well for most professionals.
11) Does CKS improve salary or career growth?
It can improve your profile and interview credibility, especially when paired with real project experience. Employers value practical Kubernetes security skills.
12) What is the best next step after CKS?
Choose based on your goal: deeper Kubernetes security (same track), a broader DevOps/DevSecOps/SRE program like MDE (cross-track), or team/platform leadership capability building (leadership path).
13) Is CKS relevant for cloud-managed Kubernetes services?
Yes. Even when the control plane is managed, your workloads, access controls, namespaces, policies, images, and runtime practices still need security expertise.
14) Is CKS worth it for platform engineers?
Absolutely. Platform engineers often define guardrails and standards. CKS helps them build secure defaults for many teams.
FAQ
1) What is the main focus of the Certified Kubernetes Security Specialist (CKS)?
CKS focuses on securing Kubernetes environments across cluster setup, hardening, system hardening, microservice vulnerability reduction, supply chain security, and runtime monitoring/security. These focus areas are reflected in the DevOpsSchool CKS agenda.
2) Who should take the CKS certification training course?
It is ideal for DevOps engineers, SREs, cloud administrators, security engineers, platform engineers, and anyone responsible for securing Kubernetes clusters and container workloads. The DevOpsSchool target audience section lists similar profiles.
3) Is the DevOpsSchool CKS training online?
Yes. The provided DevOpsSchool CKS page lists the training format as Online Training.
4) What duration is shown for the DevOpsSchool CKS course?
The DevOpsSchool CKS page shows a course duration of 10–15 hours.
5) What are the most important topics to practice hands-on before attempting CKS?
Hands-on practice is most important for RBAC, network policies, secrets handling, cluster hardening tasks, image/supply-chain checks, and monitoring/audit-related security visibility.
6) Can software engineers (not only admins) benefit from CKS?
Yes. Software engineers who deploy services on Kubernetes gain better understanding of secure deployment, secrets, microservice communication, and safer runtime behavior.
7) What comes after CKS if I want a wider career path?
A broader DevOps + DevSecOps + SRE path such as the Master in DevOps Engineering (MDE) is a strong next step for many professionals who want cross-functional growth.
8) Is CKS valuable for Indian and global job markets?
Yes. Kubernetes security skills are useful globally because Kubernetes is widely used in modern cloud-native environments. CKS helps demonstrate practical security capability in a high-demand technical area.
Conclusion
The Certified Kubernetes Security Specialist (CKS) is one of the most practical certifications for engineers and managers working with Kubernetes-based systems. It is not just about passing a certification. It is about learning how to secure real environments—clusters, workloads, images, secrets, and runtime behavior—using a structured and production-focused mindset. If your team uses Kubernetes, CKS can improve both your technical confidence and your operational security maturity. For long-term growth, pair CKS with a broader path in DevOps, DevSecOps, and SRE (such as MDE) so you can move from individual execution to platform-level and leadership-level impact.